Unlocking the Power of AWS IAM: Navigating the Access Management Menu - PART TWO
Since my exposure to AWS, I have been fascinated with how it can secure all the separate account environments. This sparked my interest in researching and studying every aspect of AWS Security, which I am now dedicated to presenting in an easy-to-understand manner. Welcome, cloud aficionados, to my journey through the expansive world of Amazon Web Services (AWS), particularly in the security area.
Today, we embark on an adventure to uncover the hidden treasures within the IAM menu of AWS, which, like a key to a secret door, can unleash the full potential of your infrastructure. So, buckle up, as we delve into the realm of access management like never before!
Unveiling the IAM Menu
Without any hesitation, there are two ways of accessing an AWS account:
- Root User
- IAM User
The Root User can be viewed as a Super Admin User that creates the initial environment of a single AWS Account. You have heard the saying:

The Root User is like a mini-god inside an AWS Account. Thus, it is recommended NEVER TO USE IT for day-to-day Operation. This is where the second type of access becomes useful called IAM User. An IAM User has privileges given to it by the Root User. It helps to avoid the temptation of using the Root User for day-to-day activities. More about the pros and cons of these two users.
Now let us examine the basic menu of the Access Management Insider an AWS IAM account
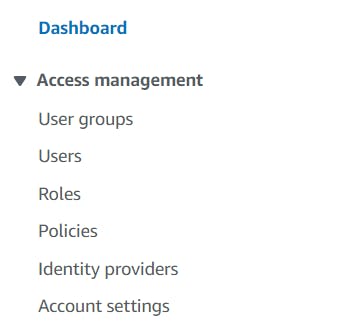
As we enter the realm of AWS IAM console, we encounter a bewitching spectrum of choices. Resembling a skilled director brandishing his wand, the IAM menu coordinates the symphony of admission controls within your cloud ecosystem. Every alternative in the menu has a distinctive aim, and collectively, they coordinate to guarantee the highest level of safety and tractability of your AWS assets.
Groups: Building the Ensemble
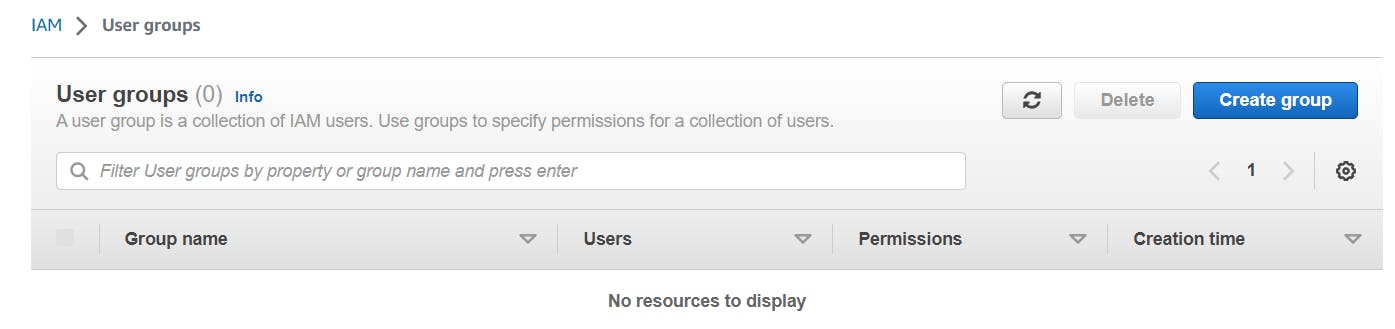
We kick things off by introducing IAM Groups. These are collections of IAM Users who share common access requirements. By assigning permissions to Groups instead of individual Users, you can streamline access management and avoid the cumbersome task of assigning permissions to each user separately. IAM Groups bring harmony and efficiency to the IAM symphony, making it easier to manage permissions across your organization.
I believe we can stop here as we have given an eagle overview of the menu of IAM. But wait, we still have two extra menus that are worthy of mentioning.
IAM Users: The Cast of Characters
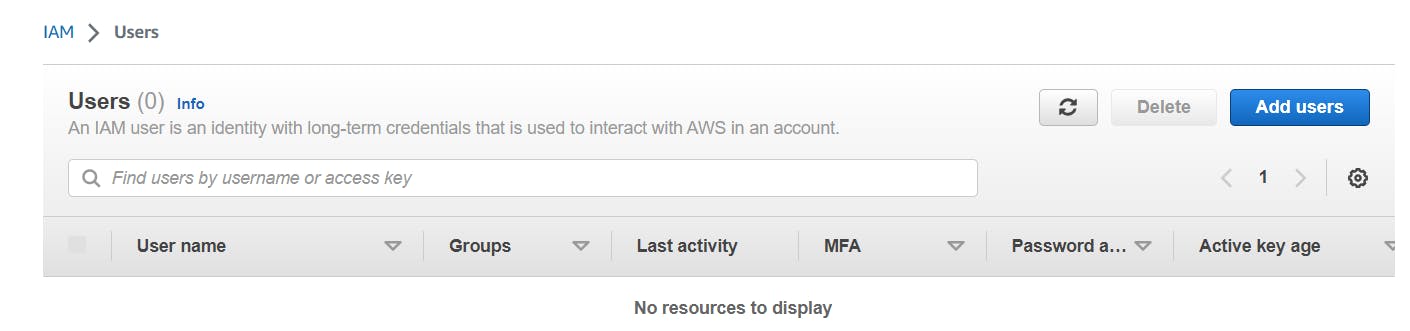
On our journey's initial leg, we get acquainted with the concept of IAM Users. These distinct identities are the ones that engage with your AWS framework, including human administrators, servers, or applications. IAM Users are the performers in this online stage, and their involvement enables the delegation of permissions, roles, and access levels in adherence to the principle of least privilege.
Roles: Shapeshifters of Access
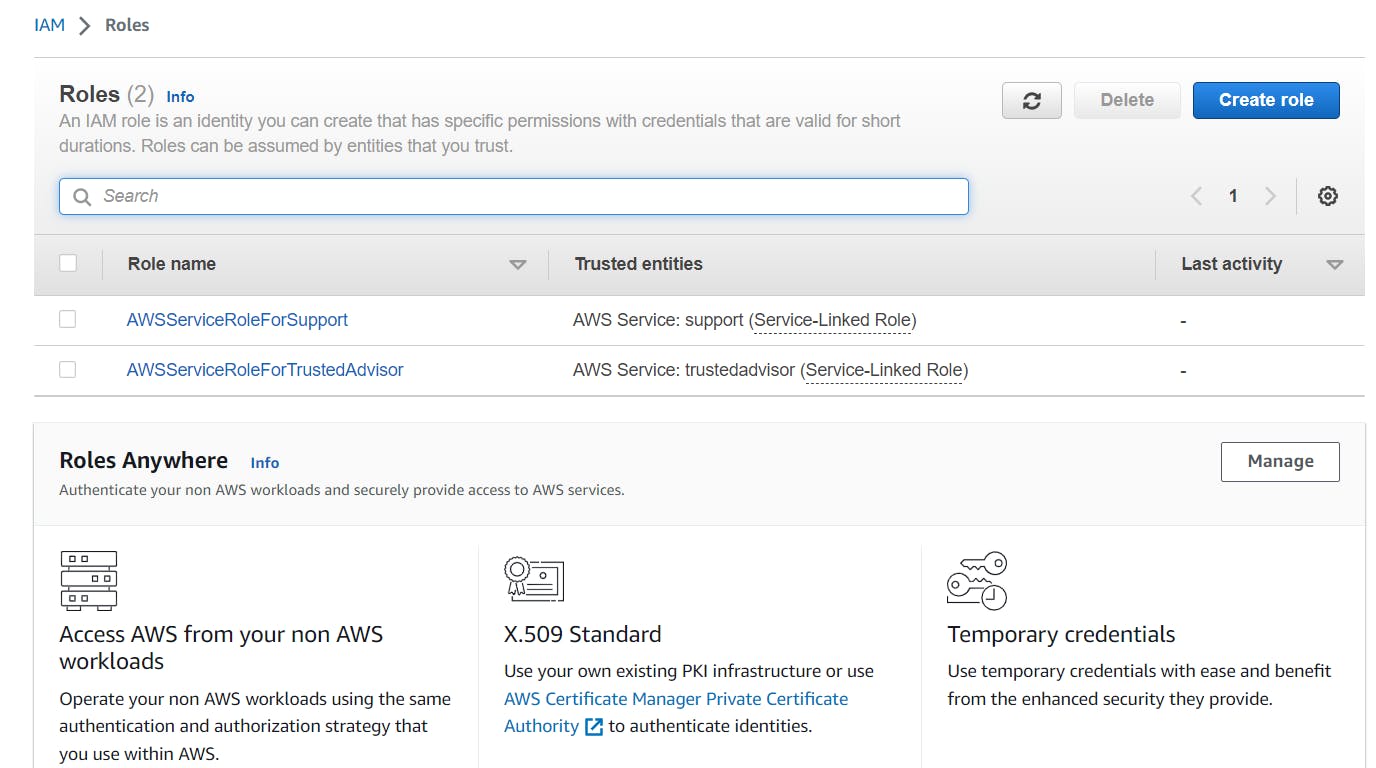
Next up, we'll be delving into IAM Roles - the metamorphic beings that inhabit the IAM menu. These Roles bestow short-term authorization to users or AWS offerings, enabling them to assume different identities with distinctive degrees of clearance. Much like a seasoned thespian, IAM Roles offer precise authority over access while still ensuring security. They effortlessly switch between various personas, making them a priceless addition to the larger game of access management.
Policies: The Scripts of Authority
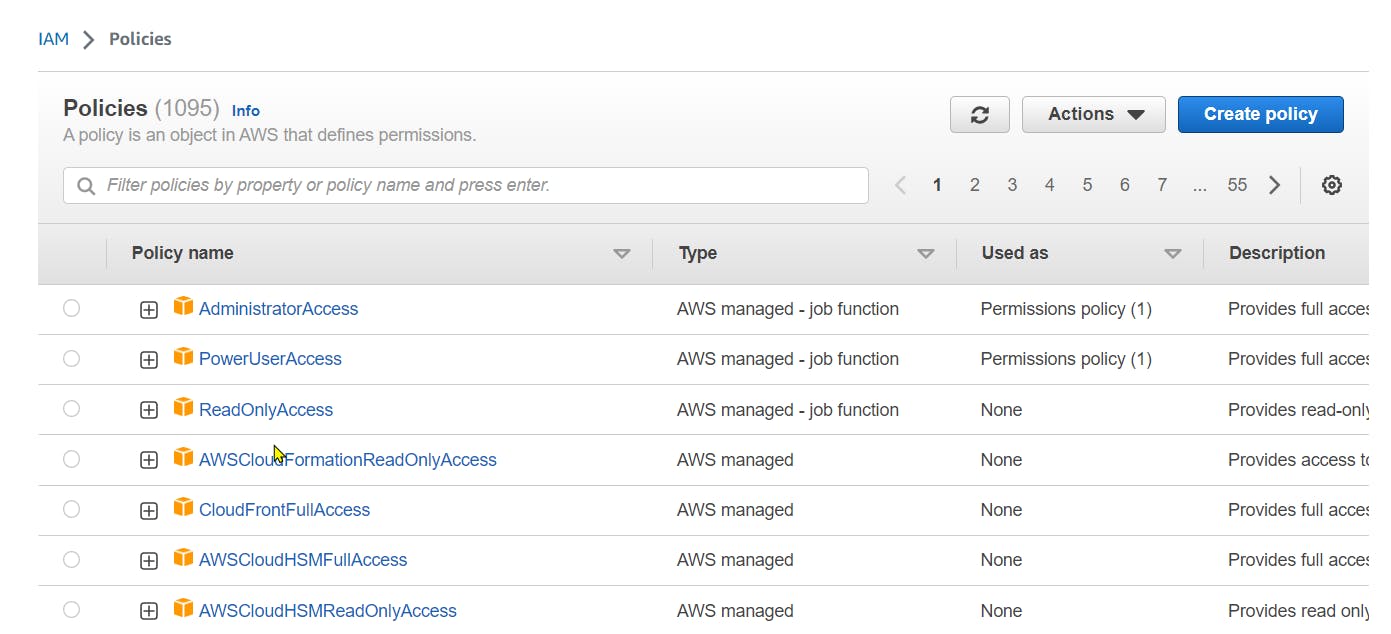
Behind every great IAM User and Role, there is an IAM Policy. These powerful documents define the rules and permissions that govern access to your AWS resources. Think of them as the scripts that guide the actors' performances, ensuring they adhere to the desired security policies. IAM Policies grant or deny access to specific resources, creating a finely tuned masterpiece of control within your cloud environment.
Identity Providers: Bridging the Gap
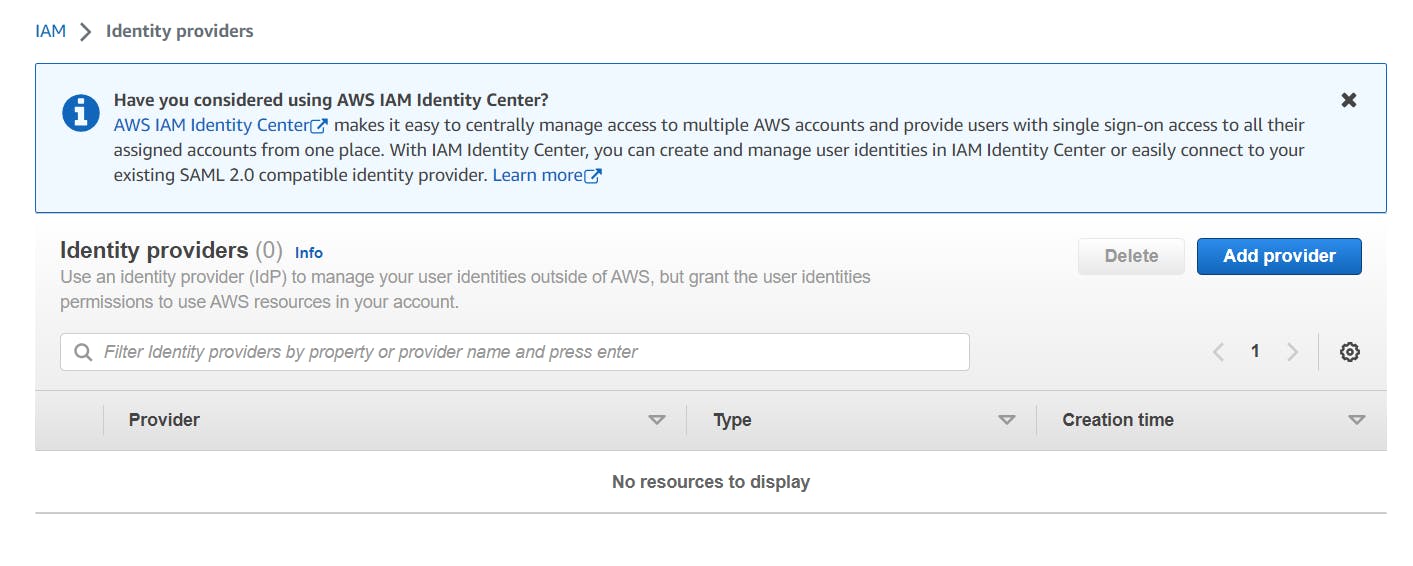
Let us delve into the fascinating world of Identity Providers (IdPs) within the AWS IAM menu. IdPs serve as the bridge between your existing identity systems and AWS, allowing you to federate identities and enable single sign-on (SSO) capabilities. With IdPs, you can seamlessly integrate your organization's authentication mechanisms, such as Active Directory or social identity providers like Google or Facebook, with AWS. By leveraging the power of Identity Providers, you can simplify access management, enhance user experience, and maintain a centralized identity management approach across your ecosystem.
IdPs act as the maestros of authentication, orchestrating the verification process and validating user identities. They enable users to log in to the AWS Management Console and access AWS resources using their existing credentials. By connecting your identity systems to AWS through Identity Providers, you can eliminate the need for separate credentials and simplify user access management.
Account Settings: Fine-Tuning Your IAM Experience
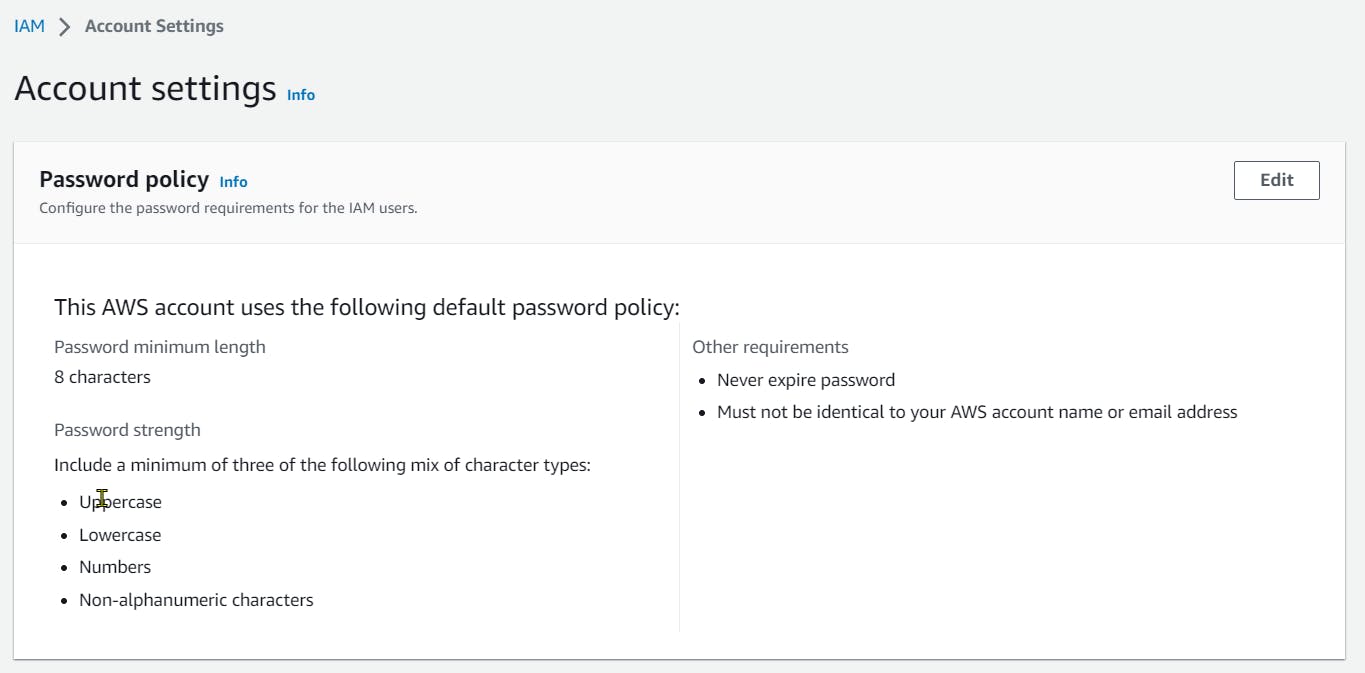
Finally, we turn our attention to the Account Settings section of the IAM menu. Account Settings provide a plethora of options to fine-tune your IAM experience and enhance the security and usability of your AWS account.
Within Account Settings, you can configure various parameters, such as password policies, multi-factor authentication (MFA) requirements, and credential rotation settings. These settings allow you to enforce strong password requirements, requiring users to create complex and unique passwords. By enabling MFA, you add layer of security, ensuring that even if an attacker manages to obtain a user's password, they would still need the second factor, such as a physical token or a mobile app, to gain access.
Furthermore, the Account Settings menu enables you to manage API access for your AWS account. You can generate and rotate access keys, granting programmatic access to your AWS resources. This feature is particularly useful for developers and applications that interact with AWS through APIs.
In addition, Account Settings allow you to set up and manage service-specific settings, such as the IAM roles for AWS services. These roles define what actions AWS services can perform on your behalf, granting them the necessary permissions while keeping your account secure.
Note: AWS constantly changes its interface. These screenshots were taken in 2023. Just putting this out so that you don't get confused along the way, especially in the future.
Congratulations! You have now witnessed the grand spectacle that is the AWS IAM menu. By exploring IAM Users, Roles, Policies, Groups, Identity Providers and Account Settings, you have unlocked a world of possibilities in access management. Remember, the key to a successful cloud journey lies in the effective management of access and permissions. So, go forth, my friends, and wield the power of IAM to protect your resources and embrace the limitless potential of AWS!

